If you share most of your meal photos with your fellow Instagram friends, or if you like to express your frustration on social media comment sections, you may find yourself in 40 % of internet users who have regretted posting their personal information on social networks. The social media account has been a source of targeting social media users by many unidentified and seemingly harmful entities.
A seemingly safe social media environment has a memory like an elephant, meaning that everything you ever posted online can bite you back a few years later and bring you long-term legal issues. What’s more, there are numerous ways you can be identified through social media, even when you think you’re not revealing anything too personal.
Thus, we gathered a list of some of the most common threats social media users face and the easiest ways to protect your social media credentials and minimize the exposure of sensitive information that may hurt you in the long run.
SOCIAL MEDIA SECURITY RISKS
Data harvesting
Artificial intelligence is becoming smarter every day, and to feed those hungry machines, scientists need vast amounts of data.
According to the old saying – the only free cheese is in the mousetrap. It’s the same with social media – even though we think it’s free, social networks are continually harvesting our data and using it to improve their algorithms and new products and services. Information you would never think of as relevant can turn out to be of great importance. Hence, you should thoroughly read terms and conditions on every social network before signing up to see how much data they collect, for how long they’re keeping it, and what they’re using it for.
Account hacking
Although everyone can be a victim of account hacking, business social media accounts are more lucrative targets since they have access to a broader audience. According to ZeroFox research, business social media accounts face takeover attempts nearly 30 times per year. Once hackers take over the account, they can wreak havoc and bring significant reputational damage and even legal issues.
Phishing attacks
Cybercriminals are continuously developing new phishing techniques, and it’s impossible to keep track of them. For instance, Instagram phishing most commonly begins with a legit-looking login page. After providing the fake page with their password and user ID, users will get transferred to the actual Instagram login page, and most of them won’t even notice that they’ve been scammed.
HOW TO PROTECT YOUR SOCIAL MEDIA ACCOUNTS

1. Keep an eye on your credentials
According to DataProt research, 53 % of people rely purely on their memory when storing passwords, while 51 % use one password across multiple accounts. Also, most of our passwords are created in a rush and contain guessable information like birth dates and pet names.
Since entrusting social media accounts with your memory isn’t the best idea, you should consider using a password manager. Password managers have generating options, and they’ll create highly secure passwords for you. Moreover, most of them nowadays store data in the cloud, meaning that you won’t lose your credentials even if your device gets stolen or lost. Also, all credentials stored on your password manager will automatically get encrypted, preventing third parties from fiddling with your data.
2. Add two-factor authentication
A solid password is an important component of a secure cybersecurity strategy, but it isn’t enough to protect your credentials. If you want to boost your security framework then choosing two-factor authentication is a good start.
In most cases, it includes a standard password in combination with a code received in a text message. You can choose a third-party 2FA provider to protect your credentials, or you can use 2FA features that are already present within your social media account.
For instance, Facebook offers its users the option to choose between text message or app authentication. At the same time, Twitter, alongside these two, can protect your account with a security key, while TikTok will ask you if you want to receive your verification code via email or an SMS message.
This way, even if hackers break through your password, they’ll have a difficult time breaking through the different layers.
3. Turn on notification for suspicious login attempts
After the Cambridge Analytica scandal in 2018, social networks started putting additional effort into protecting their users’ privacy. One of the most widely used means of protection across social media is suspicious login attempt notifications. This is when someone tries to log in to your account from an unknown device, you’ll then receive a notification. If you don’t recognize the activity, you’ll be able to block further access. This form of defense has been found to prevent numerous brute force attacks and protect users’ sensitive data.
4. Update your privacy settings
We often share our most private moments with our loved ones across social media. But we often don’t consider the downsides of our data sharing.
Thus, you should read the privacy conditions regardless of what you’re signing up for. But you should be especially careful when dealing with social media. Social networks tend to change their privacy conditions quite often. Thus, you also need to keep track of any changes that may affect you. Privacy settings are in consideration to give users the opportunity to at least partially track what’s happening with their data. This helps them to choose whether they want to give consent for data collection and use of their personal information.
5. Create a separate email account for social networks
Having multiple email accounts and keeping an eye on all of them can be demanding, but it can significantly upgrade your cybersecurity game. The best practice is to create a separate email account for your social media. Make sure that you don’t connect your banking account to this email and keep your business-related accounts separated as well. Otherwise, if hackers gain access to your social media accounts, they can break into your banking and business accounts and endanger your whole company.
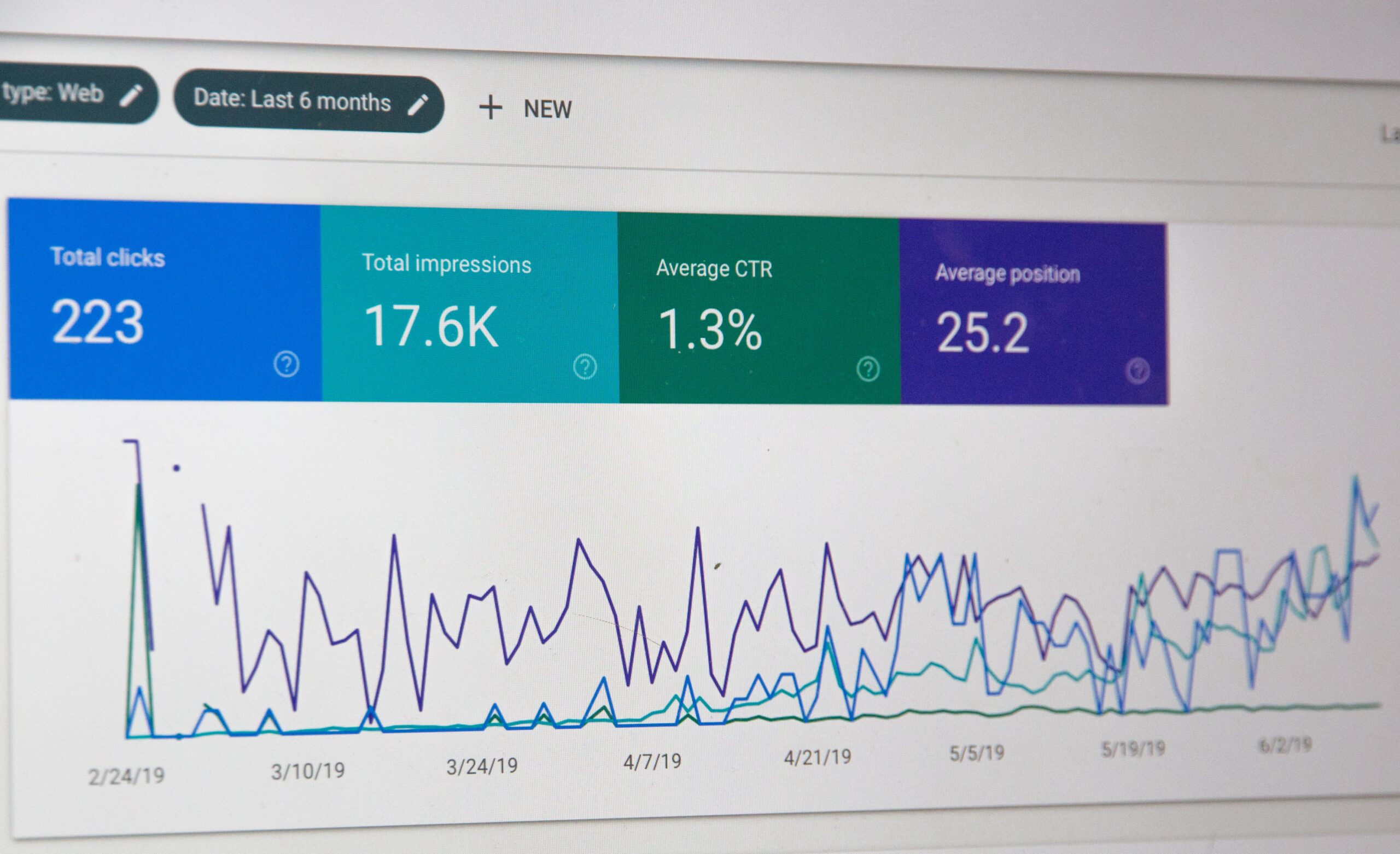
According to cybersecurity experts, developing a solid security framework isn’t a sprint; it’s a marathon. There’s a lot to consider, and every cybersecurity plan should be tailored to your specific needs. The first step should always be assessing potential risks and points of exposure. After that, implement security measures that align with your online habits and keep your plan updated regularly. Just as important is knowing whether your efforts are actually paying off if you’re curious about how much you’re really saving by staying protected, you can now calculate cybersecurity return on investment using simple tools that help you understand the value of your protection in real terms.
Staying alert, practicing good habits, and being smart with your credentials can go a long way in keeping your social media presence safe from evolving digital threats.
Drop your thoughts in the comments below.
Your email address will not be published. Required fields are marked *